HOW CHINA BROUGHT DOWN THE U.S. EMPIRE WITHOUT FIRING A SHOT
If you want to understand WWIII, you have to look at the Terrain of Finance
“All warfare is based on deception. Hence, when we are able to attack, we must seem unable; when using our forces, we must appear inactive; when we are near, we must make the enemy believe we are far away; when far away, we must make him believe we are near… If your enemy is secure at all points, be prepared for him. If he is in superior strength, evade him. If your opponent is temperamental, seek to irritate him. Pretend to be weak, that he may grow arrogant. If he is taking his ease, give him no rest. If his forces are united, separate them. Attack him where he is unprepared, appear where you are not expected.
―Sun Tzu, The Art of War
“In the near future, information warfare will control the form and future of war. We recognize this developmental trend of information warfare and see it as a driving force in the modernization of China’s military and combat readiness. This trend will be highly critical to achieving victory in future wars.”
-Unrestricted Warfare, 1999 book by two colonels in the People’s Liberation Army of China
Hey Folks,
I have been predicting the collapse of the U.S. Dollar since I was in high school. My big question since 2008 is “What’s taking so long?”
Well, I’ve been doing a bunch of research into economics lately and came across a very interesting book called The Death of Money by James Rickard, and things are making a lot more sense to me now than they did before.
According to his Amazon profile, James Rickard is a “a portfolio manager, lawyer, and economist, and has held senior positions at Citibank, Long-Term Capital Management, and Caxton Associates.” After 9/11, he was recruited by the C.I.A. to help investigate insider trading which occurred immediately prior to the attacks. He would go to consult with the agency for years to come.
In other words, he’s about as far from an anarchist as you can get. But sometimes you learn more from enemies than from allies.
The Death of Money was published in 2014, but it is more insightful than the vast majority of contemporary geopolitical discourse.
Its Amazon listing explains:
The international monetary system has collapsed three times in the past hundred years, in 1914, 1939, and 1971. Each collapse was followed by a period of tumult: war, civil unrest, or significant damage to the stability of the global economy. Now James Rickards, the acclaimed author of Currency Wars, shows why another collapse is rapidly approaching—and why this time, nothing less than the institution of money itself is at risk.
I am posting a chapter from The Death of Money because it helped me to understand that WWIII has been raging since at least 2012, and one of its key terrains is finance.
Remember when Obama said that the only alternative to a deal with Iran was war? He wasn’t wrong. It didn’t have anything to do with nuclear weapons, though. It was about sanctions.
Hopefully you find this analysis instructive. If you do, please let me know is the comment section.
And if you haven’t already subscribed, I would greatly appreciate it if you would do so.
Thanks!
Crow Qu’appelle
THE WAR GOD’S FACE HAS BECOME INDISTINCT
by James Rickard, excerpted from The Death of Money (2014)
If it’s possible to start a war in a computer room or a stock exchange that will send an enemy country to its doom, then is there non-battlespace anywhere? If a young lad setting out with his orders should ask today, “Where is the battlefield?” the answer would be, “Everywhere.”
-Colonel Qiao Liang and Colonel Wang Xiangsui of the People’s Liberation Army, China 1999
Now our enemies are also seeking the ability to sabotage our financial institutions. We cannot look back years from now and wonder why we did nothing in the face of real threats to our security and our economy.
-President Barack Obama February 12, 2013
One purpose of war is to degrade the enemy’s will and economic capacity. Surprising as it may sound, wealth destruction through a market attack can be more effective than sinking enemy ships when it comes to disabling an opponent. Financial war is the future of warfare, and no one works harder to see the future than senior Defense Department official Andy Marshall.
Seated at a table in a secure Pentagon conference room on a rainy fall morning in September 2012, Marshall moved forward in his chair. Around the table were three prominent investment managers, three SEC officials, and several think-tank experts, along with members of Marshall’s staff. Our carefully selected group was there to discuss financial war.
“That’s interesting,” Marshall said. What prompted his comment, after an hour of complete silence on his part, was our discussion of China’s stockpiling of gold and its possible use as a financial weapon in undermining the dollar’s exchange value.
Andy Marshall is called “Mr. Marshall” even by associates as a sign of respect, and at ninety-two years of age, he has earned the deference. His official title is Director of the Office of Net Assessment in the Office of the Secretary of Defense. Unofficially, he is the Pentagon’s chief futurist, the man responsible for looking over the horizon and assessing threats to U.S. national security long before others even know they exist. Marshall has held this position since 1973, through eight presidential administrations.
His involvement in national security strategy goes back even further, to 1949, when he joined the RAND Corporation, the original think tank. The list of his former associates and protégés includes Herman Kahn, James Schlesinger, Don Rumsfeld, Dick Cheney, Paul Wolfowitz, and other giants of national security policy over eight decades. Only the late Paul Nitze is comparable to Marshall in terms of the depth and breadth of his influence on strategic affairs in the period since World War II.
If Marshall is less known to the general public than the figures to whom he is compared, that is quite by design. He almost never gives interviews or speeches; nor does he appear in public, and his writings are mostly classified. In a meeting, he has a sphinxlike demeanor, listening for long periods in complete silence, occasionally uttering a few words that show he has absorbed everything and is now thinking three moves ahead.
While most Americans have not heard of Andy Marshall, the Chinese military have. Marshall was a leading theorist of the late twentieth-century “revolution in military affairs” or RMA, which presaged radical changes in weaponry and strategy based on massive computing power. Precision-guided munitions, cruise missiles, and drones are all part of RMA. People’s Liberation Army general Chen Zhou, the principal author of several recent Chinese strategic white papers, told The Economist:
“We studied RMA exhaustively. Our great hero was Andy Marshall in the Pentagon. . .We translated every word he wrote.”
Marshall is no stranger to potential confrontation with China. In fact, he is the principal architect of the main U.S. battle plan for war with China in the western Pacific. This classified plan, called “Air-Sea Battle,” involves blinding China’s surveillance capabilities and precision missiles, followed up with massive air power and naval attacks. On this occasion, Marshall was not being briefed on kinetic weapons or air-sea tactics.
He was hearing about sovereign wealth funds, stealth gold acquisition, and potential threats to national security caused by U.S. Federal Reserve policy. China has over $3 trillion of investments denominated in U.S. dollars, and every 10 percent devaluation in the dollar engineered by the Fed represents a $300 billion real wealth transfer from China to the United States. It is not clear how long China will tolerate this raid on its accumulated wealth. If China were not able to defeat the United States in the air or on the sea, it could attack through capital markets.
The threats discussed with Andy Marshall that day were entirely consistent with Chinese military doctrine. Unrestricted warfare doctrine, including financial war and cyberwarfare, has roots as far back as 1995. That year Major General Wang Pufeng, former director of strategy at Beijing’s Military Science Academy, published a paper called “The Challenge of Information Warfare.”
After paying tribute to Andy Marshall in the paper’s opening lines, Wang went on to write:
“In the near future, information warfare will control the form and future of war. We recognize this developmental trend of information warfare and see it as a driving force in the modernization of China’s military and combat readiness. This trend will be highly critical to achieving victory in future wars.”
The People’s Liberation Army of China made this doctrine even more explicit in a 1999 book entitled Unrestricted Warfare. Unrestricted warfare tactics include numerous ways of attacking an enemy without using kinetic weapons such as missiles, bombs, or torpedoes. Such tactics include the use of weapons of mass destruction that disperse biological, chemical, or radiological elements to cause civilian casualties, and terrorize populations. Other examples of unrestricted warfare include cyberattacks that can ground aviation, open floodgates, cause blackouts, and shut down the Internet.
Note: An English-language edition of Unrestricted Warfare was published in 2000 by an obscure Panamanian publisher with a provocative subtitle: China’s Master Plan to Destroy America. It had an even more provocative cover page.
You read that right. This book was published in the year 2000, a year before the September 11th attacks on the Twin Towers.
An audio version of the book is available on YouTube.
Recently, financial attacks have been added to the list of asymmetric threats first articulated by Wang and others. Unrestricted Warfare spells this out in a chapter called “The War God’s Face Has Become Indistinct.” It was written not long after the 1997 Asian financial crisis, which cascaded into the global financial panic of 1998. Much of the distress in Asia was caused by Western bankers suddenly pulling hot money out of banks in emerging Asian markets; the distress was compounded by bad economic advice from the Western-dominated IMF. From an Asian perspective, the entire debacle looked like a Western plot to destabilize their economies. The instability was real enough, with riots and bloodshed from Indonesia to South Korea. The ill will escalated to the point of name-calling between Malaysian prime minister Mahathir Mohamad and hedge fund maven George Soros in an infamous confrontation at the IMF annual meeting in Hong Kong in September 1997.
The Chinese were less affected than other Asian nations by the panic, but they studied the situation and began to see how banks, working in conjunction with the IMF, could undermine civil society and possibly force regime change. One of their responses to the crisis was to accumulate massive dollar reserves so they would not be vulnerable to a sudden “run on the bank” by Western lenders. The other response was to develop a doctrine of financial war. The lessons of the 1997-98 crisis were summarized by two Chinese military leaders in a passage both poetic and prophetic:
Economic prosperity that once excited the constant admiration of the Western world changed to a depression, like the leaves of a tree that are blown away in a single night by the autumn wind... .What is more, such a defeat on the economic front precipitates a near collapse of the social and political order.
The Chinese are ahead of us: their doctrine of strategic financial warfare emerged in 1999 in response to the 1997 Asian financial shock. In comparison, U.S. thinking about financial warfare did not take recognizable shape until ten years later, in 2009, in response to an even bigger shock, the global financial panic of 2008. By 2012, both China and the United States had engaged in extensive efforts to develop strategic and tactical financial warfare doctrines. It was in this context that our group was summoned to brief Andy Marshall and his team on the emerging threat.
Financial warfare has both offensive and defensive aspects. Offense includes malicious attacks on an enemy’s financial markets designed to disrupt trading and destroy wealth. Defense involves early detection of an attack and rapid response, such as closing markets or interdicting enemy message traffic. Offense can consist of either first-strike disruption or second-strike retaliation. In game theory, offense and defense converge, since second-strike retaliation can be sufficiently destructive to deter first-strike attacks. This line of reasoning was the same doctrine Andy Marshall helped develop in nuclear-war-fighting scenarios during the Cold War in the early 1960s. The doctrine was called Mutual Assured Destruction (MAD). Now a new doctrine of Mutual Assured Financial Destruction was emerging. To Andy Marshall, financial weapons were new, but deterrence theory was not.
The distinction between offensive and defensive capabilities in financial warfare is not the only dichotomy. There is also a distinction between physical targets, such as exchange computers, and virtual targets, such as business relationships. Virtual targets involve business conduct based on trust. A seemingly honest entity can gain trust through patient, repetitive trading, then suddenly abuse that trust by flooding a trading system with malicious, manipulative orders.
Physical targets consist of a vast network of servers, switches, fiber-optic cable, and other message traffic channels, as well as the exchange premises themselves. It is not difficult for exchange engineers or enemies to see that disrupting one link in this electronic chain through sabotage or hacking can cause chaos and force a market closure, at least temporarily. More extensive attacks can shut down markets for weeks or even months, depending on the extent of the disruption.
The financial meltdown in 2008 was not an act of financial warfare, but it did demonstrate to U.S. officials the complexity and vulnerability of the global financial system. Approximately $60 trillion of wealth was destroyed from the peak in October 2007 to the trough in March 2009. If such a catastrophe could be caused by instruments as innocuous as mortgages, imagine how much more harm could be caused by malicious market manipulation orchestrated by experts who knew exactly how the system behaved.
Thanks to Marshall and others, there’s a growing awareness that a well-orchestrated cyberfinancial attack could be as disruptive as any traditional military assault.
The Enemy Hedge Fund Scenario
A hedge fund is the perfect cover for an intelligence operation. A malicious trader does not have to destroy a system physically in order to carry out an attack. If an enemy trader sets up a legal entity such as a hedge fund, it can open accounts with major clearing brokers and commence a pattern of ordinary trading. This trading can continue for years as the entity becomes a sleeper cell in the capital markets. In time, clearing brokers come to see the entity as a prime customer generating huge commissions, and they grant it larger lines of credit.
Hedge funds are also classic intelligence-gathering operations that seek information advantage on a continual basis. The tradecraft that intelligence agencies and hedge funds use to gather information is similar. Attending high-level professional conferences is one way to build an expert network and tap into confidential information about new products and inventions. Investing in a company gives the investor access to management. Both fund traders and intelligence agents seek such access. For hedge funds, the purpose is to acquire a trading advantage, such as an early look at a new product that will affect stock prices. For intelligence services, the purpose is to keep ahead of technological developments that will affect the relative economic power of rival states.
The hedge fund sleeper could build close relationships with many brokers around the world so that its buying power was hundreds of times its capital, once all credit lines and the notional value of derivatives were taken into account. On orders from an enemy financial command, the fund network could turn malicious. Orders to sell specific stocks such as Apple, Google, or other widely held names could come flooding in and overwhelm the market makers and buyers. A price decline could start out slowly and gather momentum until it turns into a full-fledged market panic. Circuit breakers could be tripped, but the selling pressure would not abate. Business TV channels would pick up the story, and the panic would spread.
For the enemy traders, there is no tomorrow. They are not worried about paying for their trades in a few days or in the repercussions of mark-to-market losses. Their capital might even be on its way back to banks in Beijing or Moscow, unbeknownst to the clearing brokers now handling the orders. Capital markets have certain safeguards against overnight credit risk, but no effective safeguards have ever been devised to insure against losses that arise during the course of a single day. Chinese or Russian covert hedge funds could exploit this weakness while abusing trust and credit built up over years.
The malicious attack need not be confined to cash markets. While the attackers are selling stocks, they could buy put options or short the stock in a dealer swap to add selling pressure. The malicious customer becomes like a virus infecting the dealer’s trading desk, forcing it to add to the mayhem.
Another force multiplier is to begin the attack on a day when markets are already crashing for unrelated reasons. Attackers could wait for a day when major stock indexes are already down 2 percent, then launch the attack in an effort to push markets down 20 percent or more. This might produce a crash comparable to the great two-day crash of 1929, which marked the beginning of the Great Depression.
Financial attackers can also utilize psychological operations, psyops, to increase the attack’s effectiveness. This involves issuing false news stories and starting rumors. Stories that a Fed chairman has been kidnapped or that a prominent financier has suffered a heart attack would be effective. Stories that a top-tier bank has closed its doors or that a hedge fund manager has committed suicide would suffice. These would be followed by stories that major exchanges are having “technical difficulties” and sell orders are not being processed, leaving customers with massive losses. For verisimilitude, stories would be crafted to mimic events that have actually happened in recent years. Mainstream media would echo the stories, and the panic-inducing scenarios would be widespread.
The New York Stock Exchange and the SEC claim they have safeguards designed to prevent this kind of runaway trading. But those safeguards are designed to slow down rational traders who are trying to make money and may be temporarily irrational. They involve time-outs for the markets to allow traders to comprehend the situation and begin to see bargains they might buy. They also involve margin calls designed to cover mark-to-market losses and give the brokers a cushion against customers who default.
Those mitigation techniques do not stop the financial warrior, because he is not looking for bargains or profits. The attacker can use the time-out to pile on additional sell orders in a second wave of attacks. Also, these safety techniques rely heavily on actual performance by the affected parties. When a margin call is made, it applies the brakes to a legitimate trader due to the need to provide cash. But the malicious trader would ignore the margin call and continue trading. For the malicious trader, there is no day of reckoning. The fact that the enemy might be discovered later is also no deterrent. The United States knew the Japanese bombed Pearl Harbor after the attack, but it didn’t see the attack coming until its battleships were sunk or in flames.
A clearing broker could close out the malicious account to prevent more trading, but that moves the open positions from the hedge funds to the brokers. In such circumstances, many brokers would fail, and the cascade of failure would ripple through the financial system and render the clearinghouses insolvent. The entire hierarchy of exchanges, clearinghouses, brokers, and customers could be pushed to the brink of collapse.
Sleeper hedge funds can serve another insidious purpose, acting as intelligence-gathering operations years in advance of an attack. Intelligence analysts today need more than state secrets. Economic intelligence—including plans for natural resource projects, energy discoveries, pipeline routes, and other initiatives—is just as valuable.
This information can impact commodity markets, financial stability, economic growth, and the allocation of resources by both the private and the government sectors. Such intelligence is not always known to government officials, but is known to CEOs, engineers, and developers throughout the private sector.
Once a covert hedge fund acquires a material position in a target company, it can arrange to meet that company’s management. Access to management is especially easy at small to medium-size companies that receive less attention from brokerage research departments. Companies like this are often on the cutting edge of new designs in satellites, 3-D applications, and digital imaging. Access is the key. Savvy investors pick up winks and nods and interpret hints to infer the timing and nature of the latest developments. This can continue for years as the covert hedge fund patiently builds trust, churns the account, gathers information, and spots vulnerabilities. Then, like a scorpion, the fund stings, on orders from its sovereign masters.
Skeptics claim that an intelligence or military covert operation in hedge fund form would be easy to detect because of detailed anti-money-laundering and know-your-customer rules, strictly enforced by the brokers. This objection does not withstand scrutiny. The necessary techniques for operating with cover include front companies, so-called cutouts, secret agents, cover stories, and entities layered on top of each other so that the unwitting points of contact cannot see the controlling parties. A covert hedge fund structure involves layers of legal entities in tax-haven countries offering the enemy sponsor deep cover. Professional assistance is needed from corrupt lawyers or bankers who retain innocent professionals to handle detailed work such as fund administration. Directors are recruited from the advisory companies in offshore jurisdictions that offer administration services to investors. Having innocent parties in the food chain throws counterintelligence agents off the scent.
The covert fund manager would operate in well-appointed quarters in a cosmopolitan center such as Zurich or London. The enemy managers would be highly educated professionals groomed years before by foreign intelligence agencies to perform such tasks, with business degrees from Harvard or Stanford. They would receive experience in large bank training programs at places like Goldman Sachs and HSBC, forming a cadre of sleeper finance professionals who are then given a covert assignment to manage the enemy funds.
Counterintelligence agents might happen upon such sleepers; the interception of targeted communications may reveal something of their doings. But if their operation is structured wisely by the enemy, such hedge fund plotters are almost undetectable by outsiders unless insiders betray them. Then there’s the bigger issue: Is the U.S. national security community on the lookout at all?
The World in Financial War
If all this sounds far-fetched, consider that the Chinese—and others—are already perpetrating even subtler forms of financial attack.
In January 2011 The New York Times reported that China had been a net seller of U.S. Treasury securities in 2010 after years of being a net buyer. The Times report found this selling strange because China was still accumulating huge dollar reserves from its trade surpluses and was still buying dollars to manipulate the value of its currency. The implication was that China must still be a large buyer of Treasuries, even though official data showed otherwise. The Times noted that in 2010 Britain had emerged as the world’s largest purchaser of Treasury securities, and it inferred that China had “shifted purchases to accounts managed by British money managers.” In effect, China was using London bankers as a front operation to continue buying U.S. Treasury notes while Beijing officially reported that it was selling.
Another technique China uses to disguise its market intelligence operations was reported on May 20, 2007, in The New York Times when Andrew Ross Sorkin disclosed that the China Investment Corporation (CIC), another sovereign wealth fund, had agreed to purchase $3 billion of stock in Blackstone Group, the powerful and secretive U.S.-based private equity firm.
Blackstone Group was co-founded by former Nixon administration senior official Peter G. Peterson, later chairman of both the Council on Foreign Relations and the Federal Reserve Bank of New York. The other Blackstone co-founder, Stephen A. Schwarzman, is a multibillionaire who became notorious for his sixtieth birthday party held at the New York Park Avenue Armory on February 13, 2007, just a few months before Blackstone’s sale. That party included a thirty-minute performance by Rod Stewart, for which the singer was reportedly paid $1 million. China was now buying its own front-row seat at the Blackstone party, gaining access to top management and the ability to coinvest in pending deals.
In June 2007, shortly before global capital markets began the collapse that culminated in the Panic of 2008, Schwarzman described his deal-making style: “I want war, not a series of skirmishes. ... I always think about what will kill off the other bidder.” He was referring to conventional finance; real war was the furthest thing from his mind. Yet he was already a pawn in a financial war greater in scope than his blinkered perspective allowed him to see. Self-styled global citizens like Schwarzman, who treat New York as a pit stop in their travels from Davos to Dalian, may think real war is a thing of the past, even obsolete. Similar views were advanced in the late 1920s, even as events were moving toward the greatest war in history.
Analysts praised the fact that the CIC-Blackstone deal showed that China was willing “to put its vast reserves to work outside of China.” But this emphasis on the outbound money flow ignores the inbound flow of information. It is naive not to consider that information on America’s most powerful deal machine’s inner workings is being channeled to the political bureaus of the Communist Party of China. The Chinese investment due diligence teams get a look at confidential deal target information, even on deals that do not ultimately get done. The $3 billion sale price may seem like a lot of money to Schwarzman, but it is only one-tenth of one percent of China’s reserves, the equivalent of dropping a dime when you have a hundred-dollar bill. China’s penetration of Schwarzman and Blackstone is a significant step in its advance toward East Asian hegemony and a possible confrontation with the United States. Of course, information channels are a two-way street, and firms such as Blackstone do assist the U.S. intelligence community with insights on Chinese capabilities and intentions.
MAFIA CAPITALISM 101
Hey Folks, It’s READER APPRECIATION DAY! Yeah, yeah, I know, so soon. Well, it seems like you guys really liked the last edition, so I thought I’d follow up. If you didn’t know, reader appreciation day is when I take some time to respond to comments left by readers.
The United States is not the only potential Chinese financial warfare target. In September 2012 a senior Chinese official, writing in the Communist China Daily, suggested mounting an attack on the Japanese bond market in retaliation for Japanese provocations involving disputed island territories in the East China Sea. On March 10, 2013, China hacked the Reserve Bank of Australia in an effort to obtain intelligence on delicate G20 discussions.
China’s actions in the bond and private equity markets are part of its long-term effort to operate in stealth, infiltrate critical nodes, and acquire valuable corporate information in the process. These financial efforts are proceeding side by side with malicious efforts in cyberspace and attacks on systems that control critical infrastructure, launched by China’s notorious military espionage Unit 61398. These combined efforts will prove useful to China in future confrontations with the United States.
The United States is not supine when it comes to cyberwarfare; in fact, U.S. cybercapabilities probably exceed those of the Chinese.
Journalist Matthew Aid reported in 2013 on the most sensitive U.S. cyberoperation of all, inside the National Security Agency:
“A highly secretive unit of the National Security Agency (NSA)... called the Office of Tailored Access Operations, or TAO, has successfully penetrated Chinese computer and telecommunications systems for almost 15 years, generating some of the best and most reliable intelligence information about what is going on inside the People’s Republic of China... .
TAO ... requires a special security clearance to gain access to the unit’s workspaces inside the NSA operations complex. The door leading to its ultramodern operations center is protected by armed guards, an imposing steel door that can only be entered by entering the correct six-digit code into a keypad, and a retinal scanner to ensure that only those individuals specially cleared for access get through the door. ...
TAO’s mission is simple. It collects intelligence information on foreign targets by surreptitiously hacking into their computers and telecommunications systems, cracking passwords, compromising the computer security systems protecting the targeted computer, stealing the data stored on computer hard drives, and then copying all the messages and data traffic passing within the targeted email and text-messaging systems.”
Spying operations such as TAO are far more sophisticated than the relatively simple sweeps of email and telephone message traffic revealed by Edward Snowden in 2013.
Wall Street is also improving its finance-related cyberabilities. On July 18, 2013, a securities industry trade organization sponsored a financial war game, called Quantum Dawn 2, that involved more than five hundred individuals from about fifty entities and government agencies. Quantum Dawn 2 was aimed principally at preventing attacks that would disrupt normal trading. While useful, this goal falls short of preparing for a more sophisticated type of attack that would mimic, rather than disrupt, order-entry systems.
China is not the only major power fighting a financial war. Such warfare is being waged today between the United States and Iran, as the United States seeks to destabilize the Iranian regime by denying it access to critical payments networks. In February 2012, the United States banned Iran from the US dollar payments systems controlled by the Federal Reserve and the US Treasury. This proved inconvenient for Iran, but it was still able to transact business in international markets by converting payments to euros and settling transactions through the Belgium-based SWIFT bank message system. In March 2012, the United States pressured SWIFT to ban Iran from its payments system, too. Iran was then officially cut off from participating in hard-currency payments or receipts with the rest of the world. The United States made no secret of its goals in the financial war with Iran. On June 6, 2013, US Treasury official David Cohen said that the objective of US sanctions was "to cause depreciation of the rial and make it unusable in international commerce."
The results were catastrophic for the Iranian economy. Iran is a leading oil exporter and requires access to payments systems to receive dollars for the oil it ships abroad. It is also a major importer of refined petroleum products, food, and consumer electronics such as Apple computers and HP printers. Suddenly it had no way to pay for its imports, and its local currency, the rial, collapsed. Merchants sought scarce dollars on the black market at exchange rates that made the rial worth less than half its previous value, the equivalent of 100 percent inflation. A run on the Iranian banking system commenced, as depositors tried to get their rials out to purchase black-market currencies or hard assets to preserve wealth.
The government raised interest rates in an effort to stop the run on the banks. The United States had inflicted a currency collapse, hyperinflation, and a bank run and had caused a scarcity of food, gasoline, and consumer goods, through the expedient of cutting Iran out of the global payments system.
Iran fought back, even before the escalation of US efforts, by dumping dollars and buying gold to prevent the United States or its allies from freezing its dollar balances. India is a major Iranian oil importer, and the two trading partners took steps to implement an oil-for-gold swap, whereby India would buy gold on global markets and swap it with Iran for oil shipments. In turn, Iran could swap the gold with Russia or China for food or manufactured goods. In the face of extreme financial sanctions, Iran was once again proving that gold is money, good at all times and in all places.
Turkey quickly became a leading source of gold for Iran. Turkish exports of gold to Iran in March 2013 equaled $381 million, which was more than double those of the previous month. However, gold is not as easy to move as digital dollars, and gold swaps have their own risks. In January 2013, a cargo plane with 1.5 tons of gold on board was impounded by Turkish authorities at the Istanbul airport because the gold was deemed contraband. Various reports said the plane originated in Ghana, a major gold producer, and was heading for Dubai, a notorious transshipment point for gold and currencies from all over the world. Reports from the Voice of Russia speculated that the plane was ultimately headed for Iran. Regardless of the destination, someone, possibly Iran, was missing 1.5 tons of gold.
Another source of gold bound for Iran is Afghanistan. In December 2012, The New York Times reported on a healthy triangular trade among Afghanistan, Dubai, and Iran using both legitimate transportation and illegal smuggling.
The Times reported that “passengers flying from Kabul to the Persian Gulf... would be well advised to heed warnings about the danger of bags falling from overhead compartments. One courier... carried nearly 60 pounds of gold bars, each about the size of an iPhone, aboard an early morning flight.”
As Iran expanded its gold trading, the United States was quick to retaliate. The U.S. Treasury announced strict enforcement of a prohibition on gold sales to Iran effective July 1, 2013. This enforcement was aimed at Turkey and the UAE, which had been the principal suppliers to Iran. The United States had already choked off Iran’s access to hard currency; now it was doing the same to gold. It was a tacit recognition by the United States that gold is money, despite public disparagement of gold by U.S. Federal Reserve officials and others.
Gold was not Iran’s only alternative payments strategy. The most convenient was to accept local currency payments in local banks not subject to the embargo. Iran could ship oil to India and receive Indian rupees deposited for its account in Indian banks. The use of those rupees by Iran is limited to purchases in India itself, but Indian agents can quickly adapt to import Western goods with dollars and sell them to Iranians for rupees, at high markups to compensate for the time and trouble of reexporting the Indian imports. Iran also uses Chinese and Russian banks to act as front operations for illegal payments through sanctioned channels. It arranged large hard-currency deposits in Chinese and Russian banks before the sanctions were in place. Those banks then conducted normal hard-currency wire transfers through SWIFT for Iran, without disclosing that Iran was the beneficial owner, as required by SWIFT rules. Intelligence reports indicate that the amount of hard currency on de- posit by Iran in Chinese banks alone is $27 billion. However, Iran’s ability to move these funds is circumscribed by China’s need to avoid attracting the attention of the United States in making the transfers. In April 2013 Iran requested that China make a “gift” to North Korea of $4 billion as part of China’s normal humanitarian aid flows to the Hermit Kingdom. Iran did not disclose to China that the gift was actually a payment for shipments of nuclear weapons technology from North Korea to Iran. In late 2012 the United States warned Russia and China about assisting Iran in such end runs around the sanctions, but no penalties were imposed on the Russians or Chinese and none seemed likely.
SWIFT also had no appetite for enforcement because it did not want to exclude Iran from its system in the first place; it did so only under U.S. pressure. The United States did not come down hard on Russia or China because she had more important agendas to pursue with both, including Syria and North Korea. Iran also demonstrated how financial warfare and cyberwarfare could be combined in a hybrid asymmetric attack.
In May 2013 Iranian hackers had reportedly gained access to the software systems used by energy companies to control oil and natural gas pipelines around the world. By manipulating this software, Iran could wreak havoc not only on physical supply chains but also on energy derivatives markets that depended on physical supply and demand for price discovery. These probes, described by U.S. officials as reconnaissance missions, are highly dangerous on their own. Neither the Iranian hackers nor the U.S. targets seemed to consider that such activities might accidentally trigger a market panic that even the attacker did not intend. Iran was not alone in bearing the brunt of U.S. financial warfare capabilities.
U.S. financial sanctions aimed at Syria caused the Syrian pound to lose 66 percent of its value in the twelve months from July 2012 to July 2013. Inflation in Syria spiked to an annual rate of 200 percent as a result. The Syrian government was forced to conduct business in the currencies of its three principal allies—Iranian rials, Russian rubles, and Chinese yuan—because the Syrian pound had practically ceased to func- tion as a medium of exchange. By late 2013, the financial damage in Iran led to an agreement between President Obama and Iranian president Hassan Rouhani, which eased U.S. financial attacks in exchange for Iranian concessions on its uranium enrichment programs. Iran had suffered from the sanctions, but it had not collapsed, and now it had met the United States at the negotiating table.
In particular, sanctions on gold purchases by Iran were removed, enabling Iran to stockpile gold using the dollar proceeds from oil sales. President Obama made itclear that although sanctions were eased, they could be reimposed if Iran failed to live up to its promises to scale back its nuclear programs. Still, for the time being, Iran had fought the United States to a standstill in its financial war, despite enormous disruption to the Iranian economy. The U.S.-Iranian financial war of 2012-13 illustrates how nations that could not stand up to the United States militarily could prove a tough match when the battlefield is financial or electronic.
Just as the United States found its allies in Europe and Turkey, Iran found hers in Russia, China, and India. Iran’s allies spoke openly about building new non-dollar-based banking and payments systems. Dubai had carved out a role accommodating both sides in this war not unlike Switzerland in World War II. The United States had wanted to drive Iran out of the dollar payments system, and itsucceeded. But in a case of “be careful what you wish for,” an alternative non-dollar-based payment system isnow taking shape in Asia, and gold has proved to be an effective financial weapon on its own. This cat-and-mouse game among China, Russia, Iran, the United States, and North Korea involving cash, gold, weapons, and sanctions illustrates how financial weapons have moved to the fore in strategic affairs.
The Cyberfinancial Connection
Interest in financial war is hardly confined to Andy Marshall’s office in the Pentagon. In late September 2012, the Kingdom of Bahrain played host to a private, invitation-only summit of international monetary experts to discuss the geopolitics of currencies and reserves. The three-day exercise included scenarios such as the U.S. dollar’s collapse and the rise of regional reserve currencies such as the Chinese yuan and Russian ruble. Participants included European legislators, think-tank scholars, prominent journalists, and capital markets experts.
On October 12, 2012, the Federation of American Scientists conducted a financial war game in Washington, D.C., involving alternative scenarios of a shooting war between Israel and Iran. Participants were given conventional military scenarios and then asked to assess the financial impact and show how financial weapons might be used as a force multiplier.
On October 25, 2012, the Boeing Corporation conducted a financial war game during an offsite conference in Bretton Woods, New Hampshire. The conference was held at the historic Mount Washington Hotel, famous as the site of the 1944 Bretton Woods conference that established the international monetary system, which prevailed from the end of the Second World War until President Nixon closed the gold window in 1971. Although Boeing is a corporation and not a sovereign state, its interest in financial warfare is hardly surprising. Boeing has employees in seventy countries and customers in 150 countries, and it is one of the world’s largest exporters. Boeing’s Defense, Space, and Security division builds and operates the most sensitive, heavily classified platforms for U.S. national security operations. Few if any companies in the world have as large a stake as Boeing in the possibility and implications of financial warfare.
That same month, on October 30, 2012, the National Defense University completed a one-year virtual financial war game involving contributions of six leading experts from academia, think tanks, and major banks. The sponsor for the exercise was the U.S. Pacific Command, and its findings are contained in a highly sensitive 104-page final report.
In August 2013, the Swiss Army carried out one of the most elaborate financial war games of all, called Operation Duplex-Barbara. In this exercise, Swiss troops defended their country against imagined French mobs and militias swarming over their border to recover money allegedly stolen by the Swiss banks.
Even this extensive activity and analysis of financial warfare does not encompass the full extent of the threat. Cyberattacks on U.S. infrastructure, including banks and other financial institutions, are growing and can take many forms. In one troubling instance on Christmas Eve 2011, a computer file containing personal identification information on a senior U.S. government official was hacked, and the information was downloaded. The information was then used in an effort to deplete the official’s personal bank account. The official was Mary Shapiro, then the chief regulator of all U.S. capital markets.
On April 23, 2013, a Twitter account maintained by the Associated Press was hacked and used to distribute a false message that the White House had been the target of a terror attack and that President Obama had been injured. This false message came just days after the Boston Marathon terror bombing and the dramatic manhunt and shootouts with the terror bombers. The Dow Jones Industrial Index immediately plunged more than 140 points, briefly wiping out $136 billion in wealth before recovering once the message was exposed as a fake. A pro-Syrian hacker group backed by Iran called the Syrian Electronic Army claimed credit for the attack. The hackers’ success and the market reaction demonstrated that markets are on a hair trigger and are easily crashed and manipulated by various means. It was an instructive episode for other potential attackers.
These events point toward the most dangerous kind of financial attack, one that combines cyberattacks and financial warfare in the ultimate force multiplier scenario. In this situation, a cyberattack is not used to disable U.S. capital markets; instead, the cyberinvaders take control of order-entry software to spoof sell orders by major financial institutions. The intended financial collapse is similar to the rogue hedge fund scenarios, except that no cash or capital is required. The computer is programmed to mimic an out-of-control broker trying to unload trillions of dollars in stocks, bonds, and derivatives.
This scenario is a larger, more targeted version of the August 1, 2012, Knight Capital fiasco, in which a software error caused a computer to go berserk and flood the New York Stock Exchange with phony orders. Knight accumulated $7 billion in unwanted stock positions in a matter of minutes and suffered $440 million in losses to unwind them. While the disaster was taking place, no one at Knight could identify the problem’s source, and no one thought to pull the kill switch. Finally, the NYSE, in self-defense, blocked Knight from its systems.
An even greater fiasco occurred on August 22, 2013, when the NASDAQ Stock Market was paralyzed for three hours due to computer and communications problems that have never been publicly explained. An attack from Iran’s Cyber-Defense Command has not been ruled out. In August 2012, Iran’s cyberforces destroyed 30,000 computers of oil behemoth Saudi Aramco with the Shamoon digital virus, and Iranian efforts at cyberfinancial warfare are ongoing.
In these financial warfare scenarios, an attack could be so large that the NYSE would be overwhelmed and have to close down entirely. The ensuing panic would produce hundreds of billions of dollars in paper losses.
While thinkers in the national security community have expressed concerns about financial war, officials at the U.S. Treasury and Federal Reserve routinely pour cold water on the threat analysis. Their rejoinder begins with estimates of the market impact of financial war, then concludes that the Chinese or other major powers would never engage in it because it would produce massive losses on their own portfolios. This view reflects dangerous official naiveté. The Treasury view supposes that the purpose of financial war is financial gain. It is not.
The purpose of financial war is to degrade an enemy’s capabilities and subdue the enemy while seeking geopolitical advantage in targeted areas. Making a portfolio profit has nothing to do with a financial attack. If the attacker can bring an opponent to a state of near collapse and paralysis through a financial catastrophe while advancing on other fronts, then the financial war will be judged a success, even if the attacker incurs large costs. All wars have costs, and many wars are so destructive that recovery takes years or decades. This does not mean wars do not happen or that those initiating them do not find advantage despite the costs.
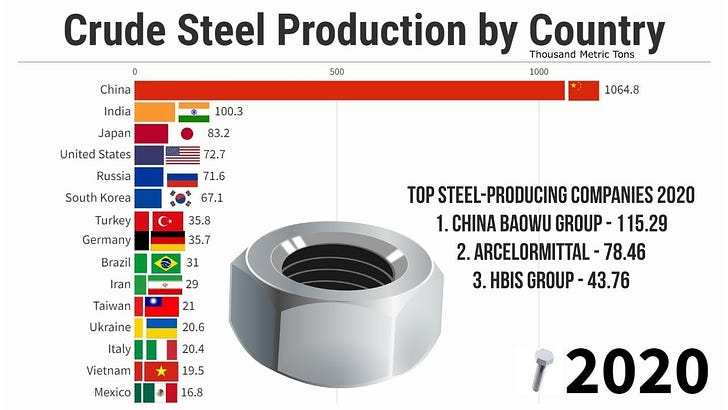
Consider the following calculations. If China lost 25 percent on the value of its reserves as the result of a financial war with the United States, the cost to China would be about $750 billion. A fleet of twelve state-of-the-art Ford-Class aircraft carriers, comparable to the envisioned U.S. carrier force, would cost over $400 billion to build and deploy once all construction, operating, overhaul, and other life-of-the-vessel costs were taken into account. The costs of securing those aircraft carriers with destroyers, submarines, and other support vessels, as well as the land-based systems and staff needed to operate the fleet, raise the costs to a significantly higher level. In short, the economic cost of confronting the United States in financial warfare may not be higher than confronting it at sea and in the air, and the damage inflicted may be even greater. China does not have a fleet of state-of-the-art aircraft carriers, but it does have cash and computers, and it will choose its own battlespace.
China could protect its reserves against asset freezes or devaluation in the event of a financial war by converting its paper wealth to gold—an option it is now pursuing aggressively. Every gold bullion acquisition by China reduces its financial vulnerability and tilts the trade-off between portfolio losses and armament costs in favor of financial war. China’s possible intentions may be inferred from its status as the world’s largest gold buyer.
The U.S. Treasury and Federal Reserve view also fails to account for intertemporal effects. An attack that is costly in the short run can be quite profitable in the long run. Whatever losses China might suffer on its portfolio in a financial war could be quickly reversed during peace talks or in a negotiated settlement. Seized accounts could be unfrozen, and market losses could be turned into gains once conditions normalized. Meanwhile, China’s geopolitical gains in areas like Taiwan or the East China Sea could be permanent, and it is the U.S. economy that might suffer most in such a contest and take years to recover.
Treasury and Fed officials dismiss concerns about financial war due to their misapprehension of the statistical properties of risk and their reliance on erroneous equilibrium models. These models assume efficient markets and rational behavior that have no correspondence to real markets. As applied to financial warfare, their view is that enemy attacks on particular stocks or markets will prove self-defeating because rational investors will jump in to buy bargains once the selling pressure begins. Such behavior exists only in relatively calm, unperturbed markets, but in actual panic situations, selling pressure feeds on itself, and buyers are nowhere to be found. A major panic will spread exponentially and lead to total collapse absent an act of force majeure by the government.
This panic dynamic has actually commenced twice in the past sixteen years. In September 1998, global capital markets were hours away from total collapse before the completion of a $4 billion, all-cash bailout of the hedge fund Long-Term Capital Management, orchestrated by the Federal Reserve Bank of New York. In October 2008, global capital markets were days away from the sequential collapse of most major banks when Congress enacted the TARP bailout, while the Fed and Treasury intervened to guarantee money-market funds, prop up AIG, and provide trillions of dollars in market liquidity. In neither panic did the Fed’s imaginary bargain hunters show up to save the day.
In short, the Treasury and Fed view of financial warfare exhibits what intelligence analysts call mirror imaging. They assume that since the United States would not launch a financial attack on China, China would not launch an attack on the United States. Far from preventing war, such myopia is a principal cause of war because it fails to comprehend the enemy’s intentions and capabilities. Where financial warfare is concerned, markets are too important to be left to the Treasury and the Fed.
Nor is it necessary to launch a financial war in order for financial warfare capability to be an effective policy instrument. It is only necessary that the threat be credible. A scenario can arise where the U.S. president stands down from military action to defend Taiwan because China has made it clear that any such action would result in the destruction of a trillion dollars or more in U.S. paper wealth. In this scenario, Taiwan is left to its fate. Andy Marshall’s Air-Sea Battle is deterred by China’s weapons of wealth destruction.
Perhaps the greatest financial threat is that these scenarios might play out by accident. In the mid-1960s, at the height of Cold War hysteria about nuclear attacks and Mutual Assured Destruction, two films, Fail-Safe and Dr. Strangelove, dealt with nuclear-war-fighting scenarios between the United States and the Soviet Union. As portrayed in these films, neither side wanted war, but it was launched nonetheless due to computer glitches and actions of rogue officers.
Capital markets today are anything but fail-safe. In fact, they are increasingly failure-prone, as the Knight Capital incident and the curious May 6, 2010, flash crash demonstrate. A financial attack may be launched by accident during a routine software upgrade or drill. Capital markets almost collapsed in 1998 and 2008 without help from malicious actors, and the risk of a similar collapse in coming years, accidental or malicious, is distressingly high.
In 2011, the National Journal published an article called “The Day After” that described in detail the highly classified plans for continuity of U.S. government operations in the face of invasion, infrastructure collapse, or extreme natural disaster. These plans include landing a helicopter squadron on the Washington Mall, near the Capitol, to swoop up the congressional leadership for evacuation to an emergency operations center called Mount Weather in Virginia. Defense Department officials would then be moved to a hardened bunker deep inside Raven Rock Mountain on the Maryland-Pennsylvania border, not far from Camp David.
Much of Marc Ambinder’s reporting involves the chain of command and what happens if certain officials, possibly including the president, are dead or missing. He points out that these contingency plans failed both during the attempted assassination of President Reagan in 1981 and again on 9/11. Recent years have seen improvement in secure communications, but serious ambiguity can still arise in the chain of command, and Ambinder says more failures can be expected in another national crisis.
HAIL TO THE RED DAWN!
Hey Folks, Today I am thinking about the triumph of good over evil, because it is Easter. I’m also thinking about the impending collapse of the Zionist-Anglo-American World Empire. It’s obviously immanent. But it seems to me that just about everyone is in denial about it.
The U.S. is No Match for Russia when it comes to Arctic Warfare
In a recent article, I raised the question of whether the U.S.´s alleged sabotage of the Russia-Germany Nord Stream pipeline means that we`re now officially in the midst of WWIII. Now, to be fair, I know a lot of my audience believes, as I do, that we now live in a globalized world where the economies of the different competing nation-states are too inte…
If the U.S. really did blow up Nord Stream, does that mean it`s officially WWIII?
On February 8th, 2023, Seymour Hersh published an investigative report into the sabotage of the Nord Stream pipeline back in September of last year. Init, Hersh makes very specific allegations about how elite U.S. Navy divers planted C4 explosives on the pipeline at Biden`s command.











The WSJ article you linked to begins: "Central banks around the world are selling U.S. government bonds at the fastest pace on record, the most dramatic shift in the $12.8 trillion Treasury market since the financial crisis." Does that really poke a hole in my theory?
Look at the chart. The selling began in late 2013, not 2010 as claimed in the 2011 NYT article. The article itself is from 2015. So the selling did not occur in 2010 as claimed. That doesn't poke any holes in your theory, it just suggests you examine your sources more closely before you publish. Unlike a potential adversary that would use that to discredit you, believe it or not, I'm actually trying to help.
So basically you agree with Trudeau... the Chinese are out to get us?
Let's see.... a nation that built itself up on cheap exports would definitely want to undermine their number one customer. Yeah, that makes sense. Of course to do so you'd want to put the profits from your trade surplus into US treasures because nothing defeats your enemy faster than supporting their bond market, right?
https://www.statista.com/statistics/246420/major-foreign-holders-of-us-treasury-debt/
As for reports of them divesting, well, the devil's in the details....
https://www.reuters.com/markets/asia/china-slips-away-treasuries-sticks-with-dollar-bonds-2023-02-22/
Granted they're heavily exposed and the US freezing Russian foreign reserves did somewhat undermine confidence, but where else can they go? The Euro? The Yen? Neither market is large enough to absorb their trade surplus. Now if Saudi Arabia can be persuaded to take Yuan instead of dollars for oil, then recycle those Yuan back into the Chinese bond market, you may have something, but it hasn't happened yet, and I suspect if they started down that road they'd end up like Iraq or Libya, both of whom tried to break away from dollar hegemony, which is why they got trashed and their leaders executed.
Now about this book, 'Unrestricted Warfare.' Let me first point out that every major military power has a plan to defeat their potential enemies. They'd be completely negligent if they didn't have one because that's what the military is supposed to do, prepare for war. That's what all these various exercises are about - preparing for war - but also demonstrating to your adversaries that you are prepared: Si vis pacem, para bellum. So nothing new there. Nothing new about Sun Tsu either. It's required reading at all military academies.
Now about the authors, Qiao Liang (乔良) and Wang Xiangsui (王湘穗).
Has anyone checked to see if they actually exist?
I find what Wikipedia (*) has to say about it very interesting.
"Taylor Fravel pointed out a common distortion in translation of the subtitle of the book. While it was translated and understood in the West by many as "China’s Master Plan to Destroy America", the actual subtitle was "Two Air Force Senior Colonels on Scenarios for War and the Operational Art in an Era of Globalization".[1]
This is also interesting:
The English translation of the book was first made available by the Foreign Broadcast Information Service in 1999.[5][2] The book was then published in English by a previously unknown Panamanian publisher, with the subtitle "China's Master Plan to Destroy America" and a picture of the burning World Trade Center on the cover.[12] A French translation was published in 2003.[13]
Foreign Broadcast Information Service? That's the CIA.
https://en.wikipedia.org/wiki/Foreign_Broadcast_Information_Service
"previously unknown Panamanian publisher" Also CIA.
I'd be very surprised if these two PLA colonels even exist. One thing about colonels: that's an operational rank. Colonels are not typically involved in strategic planning, and they definitely don't spill the beans about those plans, so I call shenanigans here.
(*) More than a few times I've seen people say "I don't trust Wikipedia and anyone who cites them is suspect" (meaning me). Wrong. Wikipedia is a valuable source of information, just not in the way most people imagine. Consider their article on neuro-linguistic programming.
https://en.wikipedia.org/wiki/Neuro-linguistic_programming
Right out of the gate they call it 'pseudoscientific' as if that isn't a giant red flag telling you it's something they don't want you taking seriously. Probably because it's a key element in psychological warfare, and you wouldn't want just anyone to know that, right?
Wikipedia gives the game away constantly with their ham-fisted attacks on anything and anyone that doesn't support the current agenda. When I'm researching a topic, it's the first place I look, and I'm hardly ever disappointed.
Now read their write-up on Unrestricted Warfare. You see any skepticism there? Any doubts as to the source of the documents? They take this book as prima facie evidence of China's intent. And from a mere couple of Colonels, no less!
https://en.wikipedia.org/wiki/Unrestricted_Warfare
As for James Rickards, once again Wikipedia:
https://en.wikipedia.org/wiki/James_Rickards
I must have seen dozens of these types of books over the 20 odd years I was a stock trader. Writing an alarmist screed is par for the course if you're trying to promote your investment business. It's even called 'talking your book.' That's not to say there aren't some very sharp minds in the investment business, but this guy ain't one of them.
Look, just take the position that nothing is ever quite what it seems. You're less likely to go wrong that way than taking things at face value. At least you could ask the question, Cui Bono? Who benefits from all this nonsense about China, Russia and Iran? Not you or me, that's for sure.
I've studied all three of our so-called adversaries, and what jumps out at me is how well they've dodged every attempt to derail them, and that they've each managed to advance their social well being enormously using three very different organizing principles. What that says to me is that almost any system of social organization has a decent chance of success if it has strong leadership dedicated to national sovereignty, and is economically and militarily powerful enough to resist the Global Hegemon.
That's what all the panic is about. The NWO boys have hit a BRIC wall. No need to make it any more complicated than that.